Scan types in this section:
Packet fragmentation, source routing, source port manipulation, IP address decoy, IP address spoofing, creating custom packets, randomizing host order, sending Bad checksum.
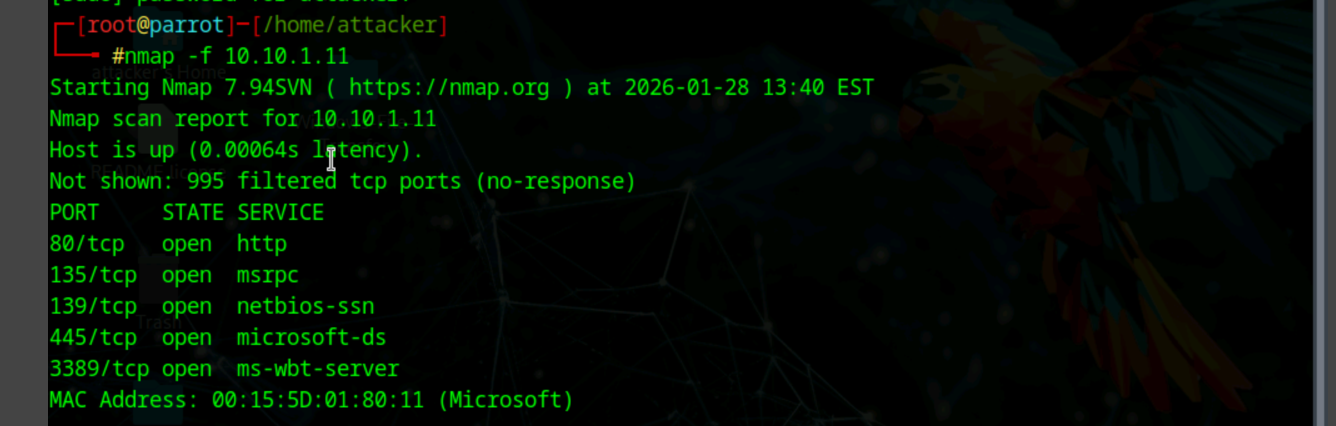
Split IP packet in fragments to avoid firewall
nmap -f [ip]
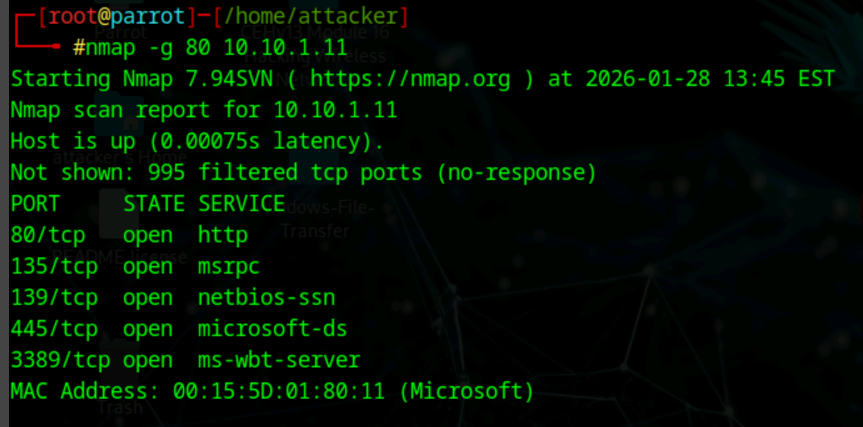
Change source port to avoid firewall (If only allows well-known ports)
nmap -g 80 or –source-port
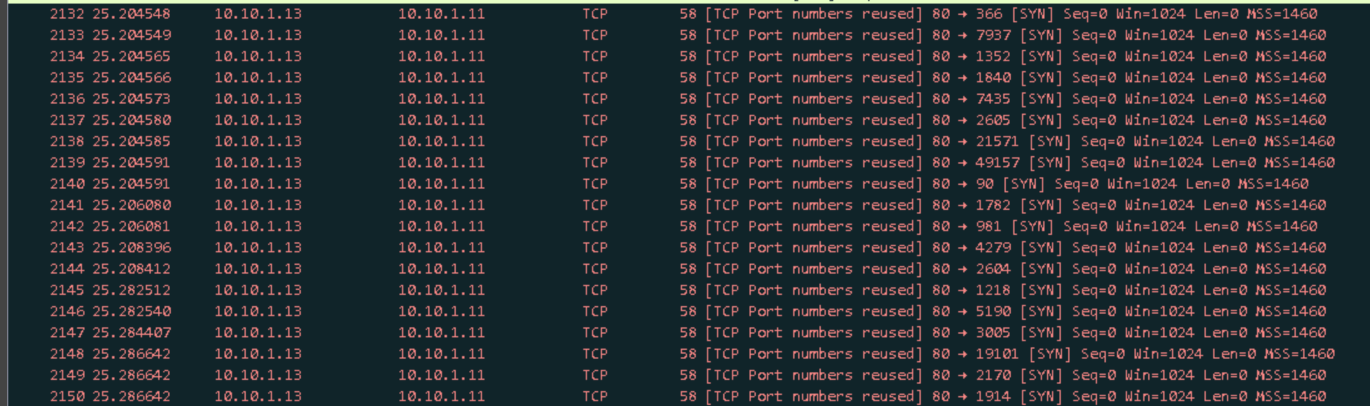
Wireshark:
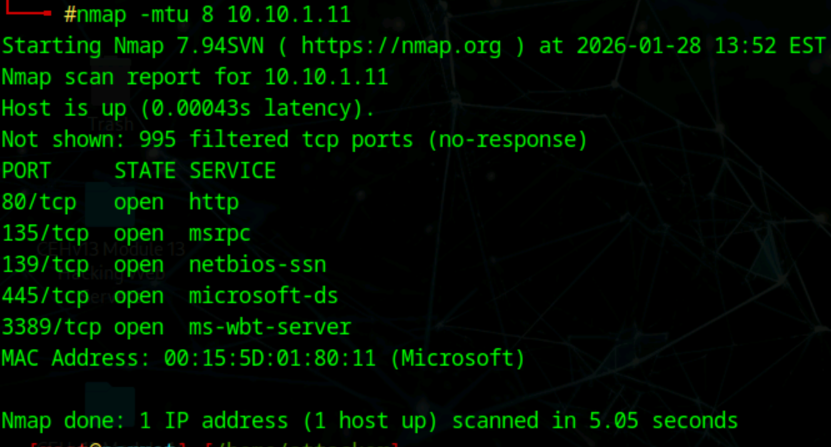
Scan using smaller MTU
nmap -mtu 8 [ip]
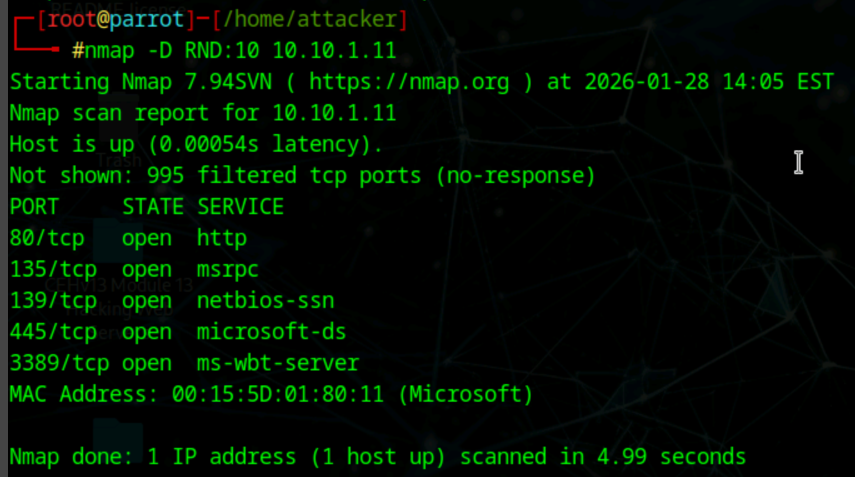
IP address decoy - makes hard for IDS to detect which IP is scanning
nmap -D RND:10 10.10.1.11